Fake profiles used the popular Strava exercise app to spy on Israeli security personnel working at sensitive sites in Israel, a new report by the Israeli FakeReporter watchdog revealed on Tuesday.
The security risks associated with the Strava app were first reported on in 2018, when The New York Times reported that analysts were warning that a "heatmap" feature on Strava which shows the running tracks of all Strava users who have made their posts public could be used to identify individual users by cross-referencing Strava data with other social media use.
The heatmap feature notably revealed the locations of military bases around the world, with signatures in American bases in countries like Afghanistan, Iraq and Syria standing out compared to their surroundings.
<br>Security concerns
The security breaches possible through the app were exacerbated with the Segment feature. Already in 2018, social media users and analysts were pointing out that the Segment feature could be used to create a list of people who travelled a certain route, including within sensitive locations.
Malicious actors could use the Heatmap to find commonly traversed routes and then create Segments along those routes to expose large numbers of users.
It is possible to hide exercise activity so it doesn't appear on the Segments feature, but to do so, users need to set each activity as "private," even if their profile in general is already set to "private."
FakeReporter, which uses crowdsourcing in order to identify, expose and disable attacks and fraudulent activity, began investigating the issue after they received a tip about suspicious activity on the Strava app. The tip revealed an anonymous profile that had uploaded artificial GPS data within IDF bases and sensitive security facilities.
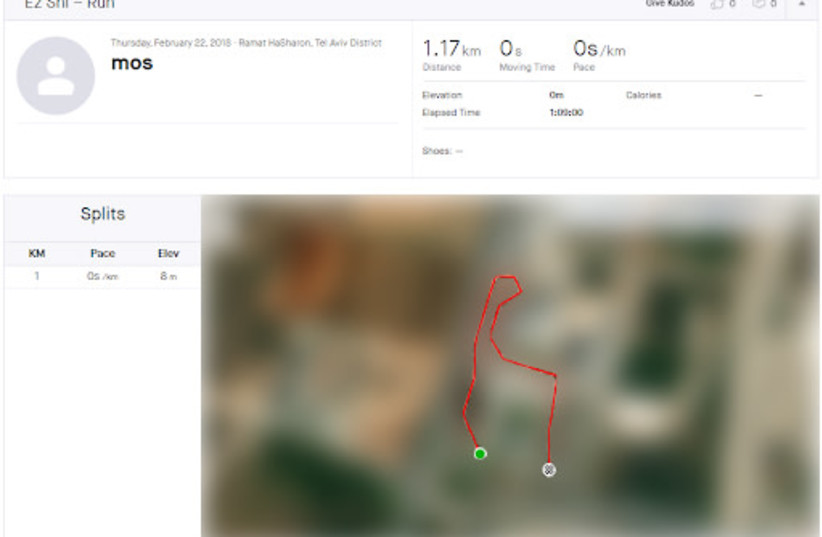
The anonymous profile, with the username "Ez Shl," created artificial Segments with the GPS data, using the Heatmap to identify the routes with the greatest chance of finding a large number of users. According to the FakeReporter report, the unique nature of the profile's activity indicates that the user intended to produce Segments in security-sensitive areas in Israel in order to collect information about people serving in those classified locations.
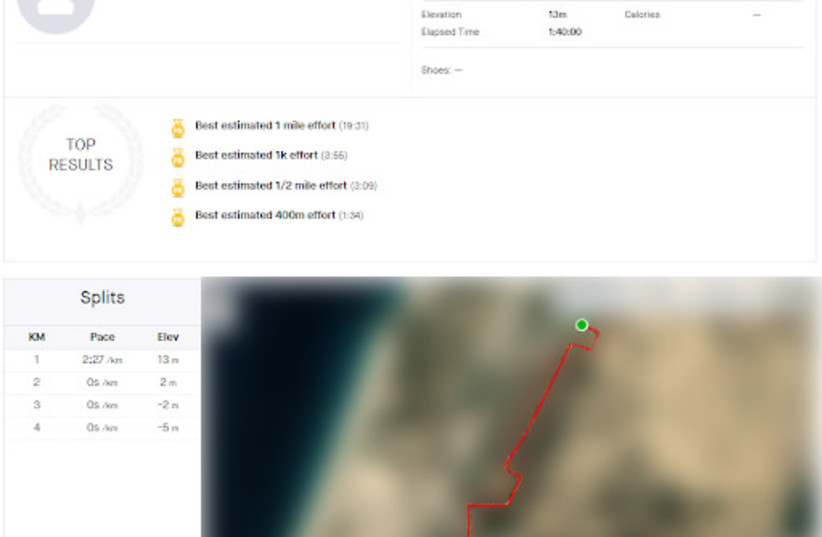
The artificial segments were located near sites such as Mossad headquarters, the Israeli Air Force's Kanaf 2 base, a base near the nuclear reactor in Dimona, the Bahad 1 base and the Palmachim base, among other locations.
Through the app, the fake profile was able to reveal their identities, locations they visited throughout the world, their relatives and colleagues, their home addresses and more. The actor was able to collect data that could threaten the State of Israel, including details about secret bases and the names and personal details of soldiers, officers and Defense Ministry officials.
The anonymous profile was active in 2019 and IDF protocols were updated in light of the breach.
FakeReporter warned that this breach could also be used by actors to collect personal information from users around the world, putting undercover personnel and sensitive security facilities at risk of exposure. The watchdog added that further research is needed to determine if this breach has already been used against other countries.
"We contacted the Israeli security forces as soon as we became aware of this security breach," said Achiya Schatz, executive director of FakeReporter. "After receiving approval from the security forces to proceed, FakeReporter contacted Strava, and they formed a senior team to address the issue."
“Despite past revelations, it does not appear that Israeli security agencies have caught up."
Achiya Schatz, executive-director of FakeReporter
“Despite past revelations, it does not appear that Israeli security agencies have caught up. Although Strava made significant updates to its privacy settings, confused users might still be exposed publicly, even if their profiles were set to ‘private,'” added Schatz. “By exploiting the capability to upload engineered files, revealing the details of users anywhere in the world, hostile elements have taken one alarming step closer to exploiting a popular app in order to harm the security of citizens and countries alike.”
"The IDF in general, with its various bodies, is aware of the threats that are developing in the world of the internet," said the IDF Spokesperson's Unit in response to the report. "In order to deal with them, and following previous incidents such as the incident in question, procedures are periodically transferred to servants in sensitive positions."
MK demand actions
After the FakeReporter report was released, MK Michal Rozin, chairwoman of the Meretz faction, contacted the chairman of the Knesset Foreign Affairs and Defense Committee Ram Ben-Barak with a request to hold an urgent discussion on the issue.
"Such a failure poses a tangible danger to the security personnel who have been exposed and the potential for enormous harm to Israel and its citizens."
MK Michal Rozin, chairwoman of the Meretz faction
"Such a failure poses a tangible danger to the security personnel who have been exposed and the potential for enormous harm to Israel and its citizens," said Rozin. "According to the reports, as early as 2018, it was revealed how the Strava application reveals a lot of information, but the procedures in the security bodies in Israel remain the same. This continuing omission, which endangers the employees of the security bodies and the citizens of Israel, can and should be stopped."
"The reality is that with the flick of a button a 'social' app can become a weapon. We live in an age where the power and size of the networks is intensifying every day but the rights and protections we deserve are not," added the Meretz MK.
