Gaza-based terrorists control a number of social media accounts claiming to be Israeli women, in an attempt to catfish Israelis and expose them to harm, the Shin Bet (Israel Security Agency) approved for publication on Monday afternoon.
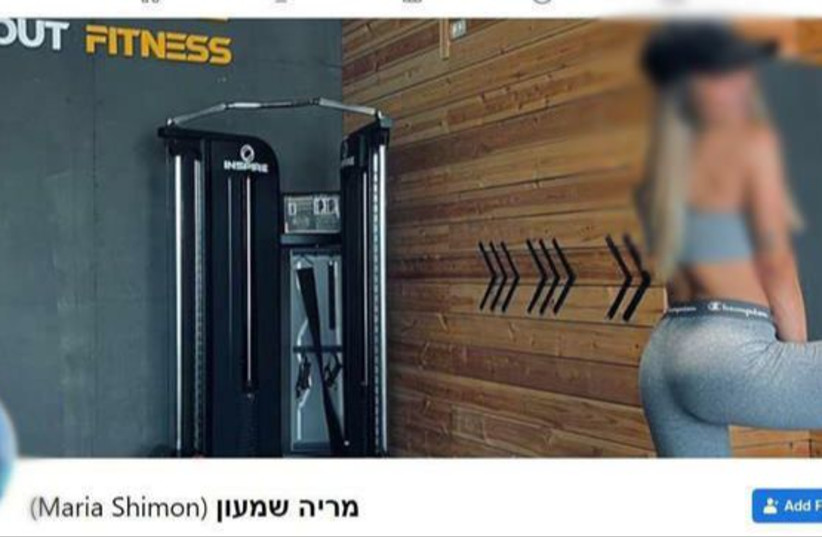
The Palestinian terrorists used photos of real Israeli women for the profiles, including several accounts detected by Shin Bet that was using the name "Maria David" or "Maria Shimon."
The accounts' owners impersonated an Israeli fitness trainer on both Facebook and Instagram, in an attempt to make contact with Israeli civilians or IDF male soldiers.
These profiles were later removed by the social media platforms following the intervention of the cyber unit in Israel's state attorney's office.
In a statement, the Shin Bet issued a warning to Israelis that terrorist groups are using social media to "lure in innocent civilians in a manner that poses a threat to their personal security." The Israeli military has thwarted several similar attempts by Hamas to honeypot troops in recent years.
Previous Hamas honeypot attempt
Two years ago, the phones of hundreds of soldiers, including combat soldiers, were compromised. The IDF thwarted the attempt by the Gaza-based terror group in an operation they called “Rebound.”
In April, an extensive fake profile network on Facebook operated by Hamas was uncovered by security forces. The network, reportedly operated by Hamas for several months, was used for surveillance and obtaining sensitive information on the targets, according to Cybereason, the US-based and Israeli-owned company that uncovered Hamas' operation, said.
The fake accounts mainly targeted young Israelis who serve in the IDF and other security establishments or Israelis who work at emergency services.
Another Hamas honeypot attempt was discovered and foiled in July, when seemingly innocent profiles operated by the Palestinian terror organization approached Israelis on Telegram and various social networks that dealt with soccer and dating and tried to implant spyware under the guise of a puzzle app.
The app would allow the attacker, Hamas, to gain almost complete control over the soldier’s device. It would then be used to gather critical information and even track the soldier.
The network was identified after a soldier reported a suspicious conversation that he had with someone on Telegram.
